Biometric Tech to Improve IoT Security
Cyber attacks against IoT devices can cause considerable damages. The US Department of Homeland Security (DHS) Science and Technology Directorate (S&T) has signed a...
Major Power Embraces Blockchain for Cybersecurity
Russia has decided to take a closer look at blockchain technology applications for security. The Russian Ministry of Defense has been launching a research...
Will Blockchain Technology Revolutionize Defense Industries?
The need for better data has been driving industries in large to adopt blockchain technology. Is blockchain going to change the global defense industry?...
Technology Powerhouse Examines Quantum Encryption
There are plenty of ways that companies and scientists are attempting to integrate the weird effects of quantum mechanics into everyday technology. One potential...
Apply Now: iHLS Startup Competition for Security, Defense and HLS
iHLS is delighted to host for the first time the prestigious Startup Competition for innovative technologies in the security, defense and homeland security fields,...
Coming Soon! Prestigious Startup Competition for Security, Defense and HLS
iHLS is delighted to host for the first time the prestigious Startup Competition for innovative technologies in the security, defense and homeland security fields,...
Ground-Breaking Startup? Apply Now to iHLS Security Accelerator
Apply Now!
Are you a disruptive startup in the security field?
We at the iHLS Security Accelerator are looking for innovative ground-breaking technologies offering solutions for...
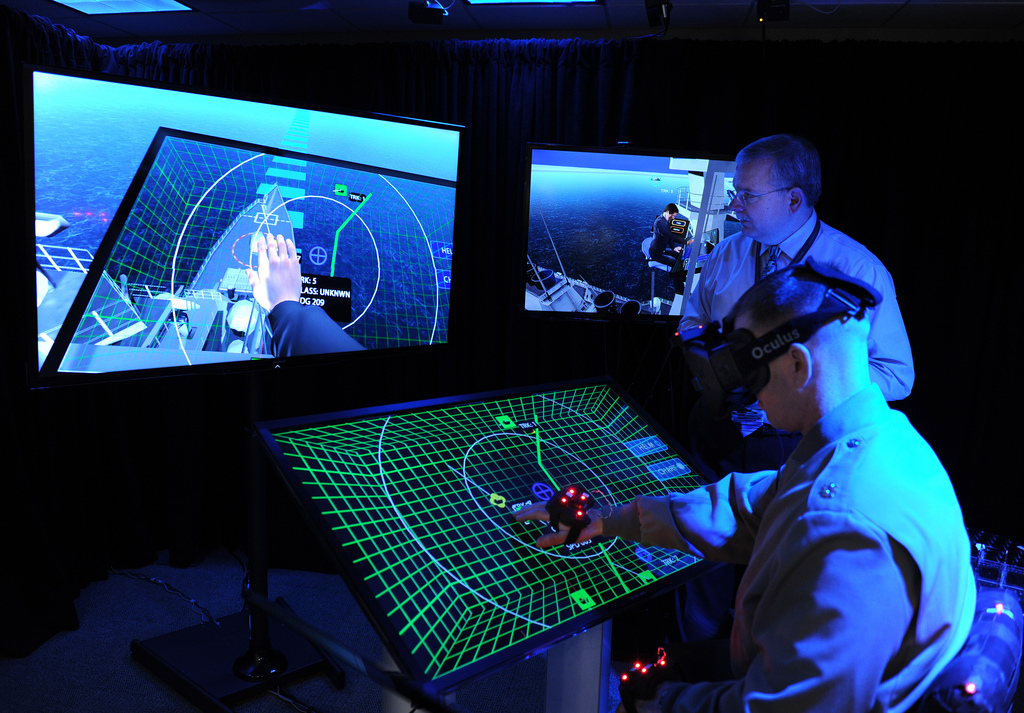
US Special Forces Receive Exceptional Video Capabilities
Video data link handheld radios were required in order to help US special forces personnel receive, transmit, and display full-motion video for situational awareness....
Startup in Security Field? Apply Now to iHLS Security Accelerator
Apply Now!
Are you a disruptive startup in the security field?
We at the iHLS Security Accelerator are looking for innovative ground-breaking technologies offering solutions for...
Law Enforcement Authorities Purchase Tech to Unlock iPhones
iPhones encrypt user data by default. Those in physical possession normally cannot access the phone’s data, such as contact list, saved messages, or photos,...
Join the Game! iHLS Security Accelerator is Opening its 5th Startup...
Apply Now!
Are you a disruptive startup in the security field?
We at the iHLS Security Accelerator are looking for innovative ground-breaking technologies offering solutions for...
Groundbreaking Tech Offers Secure Sharing of Sensitive Data
A new technology aims to help the US Department of Homeland Security (DHS) allow sensitive data to be shared and analyzed while it remains...
iHLS Security Accelerator is Looking for Next Generation Startups!
Are you a disruptive startup in the security field?
We at the iHLS Security Accelerator are looking for innovative ground-breaking technologies offering solutions for civilian...
Startup in the Security Field? Join iHLS Accelerator
Are you a disruptive startup in the security field?
We at the iHLS Security Accelerator are looking for innovative ground-breaking technologies offering solutions for civilian...
iHLS Accelerator Startup: Blockchain Based Solution to Firearms Registration
The recent wave of deadly terrorist attacks in Europe, particularly in Paris, has raised questions regarding illegal firearms, such as deactivated Kalashnikov rifles, that...
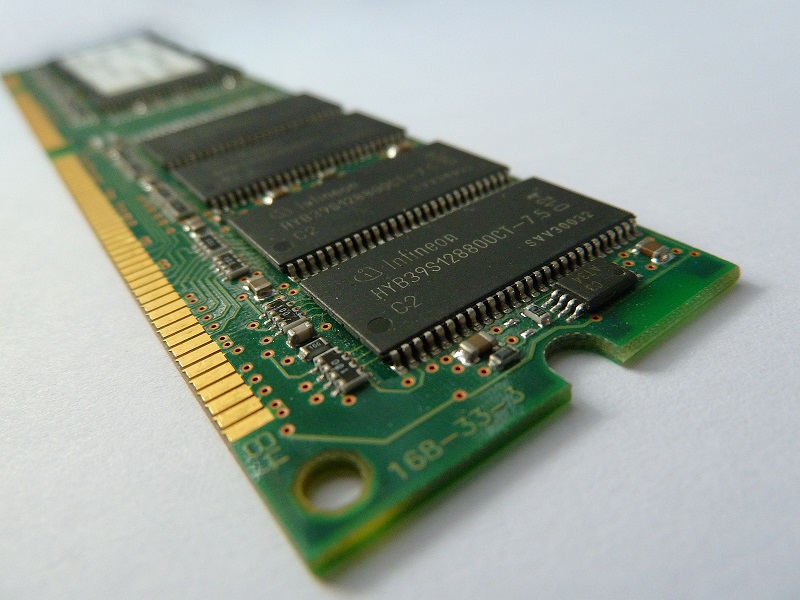
Power-Saving Chip to Revolutionize IoT Network
The IoT network is capable of connecting many different sensors integrated in civil structures, appliances, vehicles, manufacturing equipment, etc. to online servers. However, one...
Quantum Technology to Secure Autonomous Car
Autonomous vehicle technology is an emerging global market. By 2025, the partially autonomous vehicles market is expected to be at 36 billion U.S. dollars...
Autonomous Car Security Tech to Be Implemented in UAVs
With the increasing automation and widespread use of unmanned aerial systems, potential cyber-attacks on aerial fleets are already a major concern. A recent collaboration...
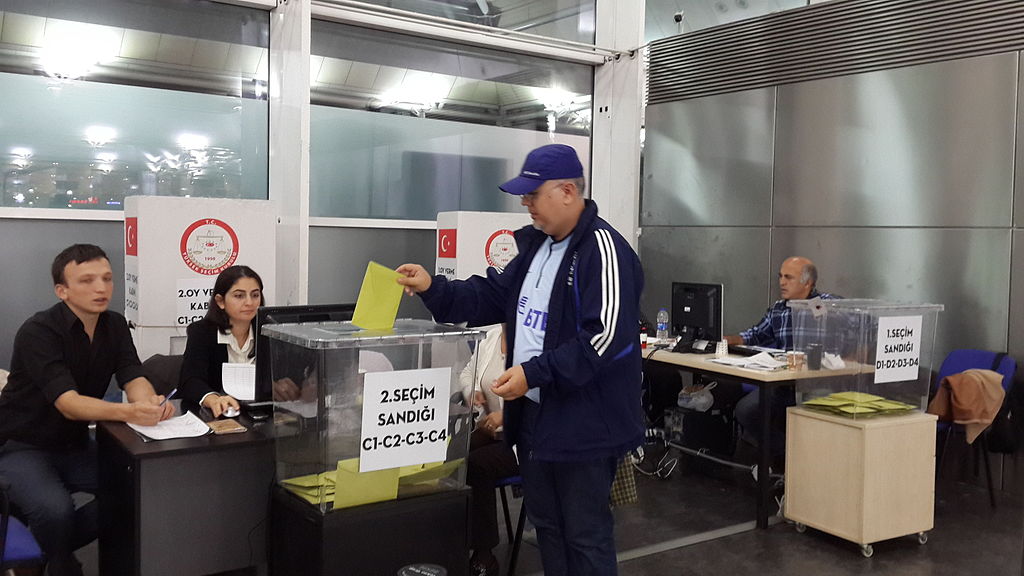
Blockchain Technology Will Be Used At Russian Presidential Elections
State-run VTSIOM will introduce cutting-edge blockchain technology for exit polls at the forthcoming Russian presidential elections. It’s designed to ensure transparency of data collection...
iHLS Accelerator is Looking for Game-Changing Technologies
We at the iHLS Security Accelerator are looking for disruptive ground-breaking technologies offering solutions for civilian defense, securing government institutions, vital infrastructure and borders,...
IoT Device Encryption Feasible with Minimal Power
The vast array of connected industrial devices, such as embedded sensors, smart lighting, and monitoring systems, requires high levels of security. Most sensitive web...
Israeli Cybersecurity at Forefront of War Against Cybercrime
The cyber incidents that dominated global headlines over the past year indicated not only a growing trend but one that is escalating in size,...