Women Suspected to Attempt Next Terror Attack
Europe is preparing for its next Islamic State-inspired terror attack to be carried out by a female assassin after a string of arrests of...
Digital Identity to Go Through Security Revolution
A national digital identity network is to be built in Canada. SecureKey Technologies and a Canadian non-profit coalition have received a grant from a...
USB-Connected Devices Are Not Secure As Thought
Security flaws found in USB-connected devices raise questions about the trustworthy of the devices. Apparently, USB connections should be redesigned to offer more security,...
IOT Security – An American Top Priority
The U.S. Department of Homeland Security (DHS) is planning to invest $1 million in five IoT security startups selected through its program Securing the...
Computer Security to Be Achieved by Mini-Mazes
As hacking techniques are constantly improving, scientists have been trying to find new ways and authentication methods to secure computers. Researchers in South Korea...
Islamic State in India – Recruitment Patterns and Technology Use
Technologically-advanced Islamist terror groups gain momentum in India. India’s intelligence agencies and state police forces coordinated to bust a hitherto unknown jihadist cell, apparently...
New Encryption Solution for Microsoft
WinMagic Inc., a data encryption firm, announced recently the availability of SecureDoc for Microsoft’s BitLocker, an intelligent key management and encryption solution that improves...
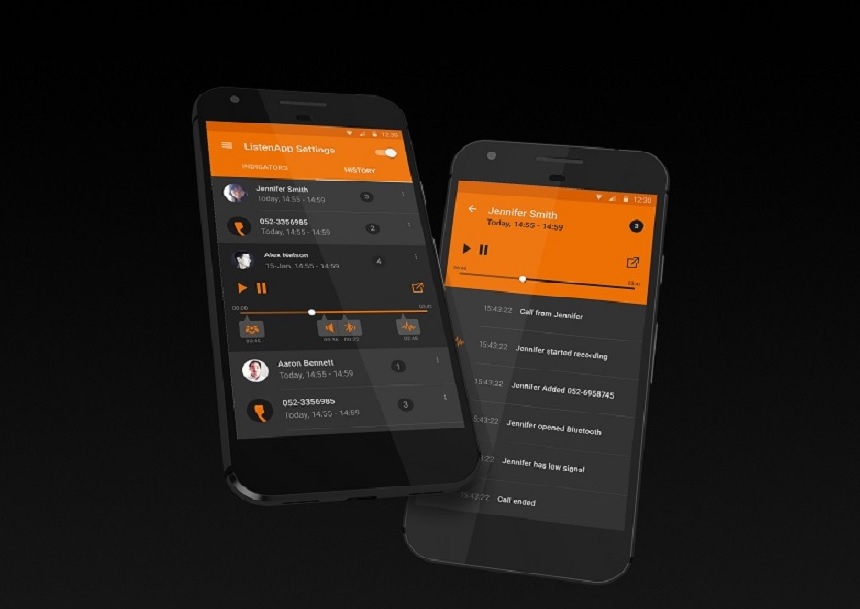
New Anti-Terror Tools Sought in Encrypted Messaging
France and Germany are insisting makers of encrypted messaging apps such as Telegram to help governments monitor communications among suspected extremists.
Privacy advocates argue that...
Current IoT Security Industry Trends
Internet of Things - IoT security breaches have been dominating headlines lately. Even if you personally don’t suffer consequences of the mediocre security of...
Defending Encryption? In France, It Could Start Costing you
A new French law would impose penalties and fines on smartphone manufacturers who refuse to hand over encrypted information to law enforcement in terrorism...
Digital Identity and Cryptographic Technology to Enhance IoT Security
Recent cybercrime and hacking exploits have shown clearly that much of the IoT – devices, services and applications – is coming online largely in...
New Emergency Function by Smartphone Giants
Apple's new operating system will come with an option to lock your iPhone's fingerprint scanner and bring up a hotline to the police. The...
Cyber Security Rules for Autonomous Vehicles Set by UK
The United Kingdom has recently published a set of cyber security regulations, “Key principles of vehicle cyber security for connected and automated vehicles”. The...
Communication Encryption Dilemma
The past few years have been rough on law enforcement agencies around the world. Online communication is encrypted most of the time, making it...
Threat Calls Against US Jewish Institutions – Using Masking Technologies
Federal investigators believe the latest wave of threat calls against Jewish centers and schools around the country was a coordinated attack perpetrated using sophisticated...
An Equivalent to License plates – for UAV’s?
AirMap, a world leader in airspace management for unmanned aircraft, recently announced a partnership with DigiCert that will enable, for the first time, instant...
Encryption Tech Enhances Marines’ Command and Control Capabilities
The US Marine Corps has been enhancing its command and control capabilities. Since July 2016, the corps has rolled out 1,100 units of its...
Will Blockchain Tech Revolutionize Cybersecurity?
With Blockchain becoming more popular these days, a significant number of US government departments are rapidly showing interest. The US Department of Homeland Security...
Device Encryption Frustrates Enforcement Agencies
The FBI had been unable to access data from 7,775 devices in fiscal year 2017, a growing figure causing setbacks in cases from terrorism...
Meet the World’s Smallest Non-Hackable Chip
The more digital the world becomes, the more hacking becomes a serious threat. The world's smallest "non-hackable" security chip that can be widely used...
The Secure Communication of the Future City
Today, mathematical algorithms are used to encrypt text messages, banking transactions and health information. Intercepting these encrypted messages requires figuring out the exact algorithm...
China’s Cybersecurity Law Influences Tech Giants
There has been a growing global trend regarding the security and sovereignty of digital data - building facilities that store online data closer to...