Billions Flow into the Tech Powering Tomorrow’s Battlefields
Artificial intelligence continues to dominate global venture capital flows, but its rise is not occurring in isolation. According to recent Crunchbase data, funding growth...
The Security Risks Behind the Internet’s First Social Network for AI...
Autonomous AI agents are moving from theory into public-facing systems, but the infrastructure around them is struggling to keep up. Platforms designed for experimentation...
When Automation Meets Poor Security Hygiene
As artificial intelligence becomes a standard feature in mobile applications, a familiar security problem is re-emerging at scale. Developers are racing to integrate cloud...
The Privacy Problem Built Into Voice Assistants
Voice-controlled assistants have become a constant presence in homes, phones, and offices, quietly waiting for a wake word before responding. That convenience, however, depends...
The Border That Watches Its Back
Modern borders are increasingly difficult to defend with traditional means alone. Fast-moving ground forces, low-flying drones, cyber interference, and long-range missiles compress reaction times...
How to Shut Off AI and Tracking Without Switching Browsers
Modern web browsers have quietly evolved from simple tools for accessing the internet into dense platforms packed with AI assistants, shopping prompts, sponsored content,...
Why Cybersecurity Works Better When Defenders Share Data
Organizations are increasingly expected to share data across corporate boundaries, yet cybersecurity risks have never been higher. As partnerships, mergers, and joint technology projects...
AI Firewall Unveiled: Is Your Network Finally Unhackable?
aiFWall Inc. unveiled an innovative solution for securing artificial intelligence systems. It is a dedicated firewall designed to protect enterprise AI deployments by using...
Cybercrime’s New Wave: Has AI Made Attacks Unstoppable?
Cybercrime is entering a phase where speed and scale are no longer limited by human skill. For years, defenders have tracked the evolution of...
Why Defense Networks Are Making Room for Generative AI
The Pentagon is accelerating its push into military artificial intelligence by integrating Grok, the generative AI model developed by xAI, into its secure digital...
The Cybersecurity Playbook Built for Grid Disruption and Geopolitical Crises
Energy infrastructure is becoming a prime target in modern cyber conflict. Power generation, transmission, and distribution systems are increasingly digital, interconnected, and exposed, while...
The Cybersecurity Shift That Treats AI as Both Weapon and Shield
Cybersecurity leaders are heading into 2026 facing a problem that is both familiar and fundamentally changed. The attack surface keeps expanding as organizations adopt...
A Cyber Defense Company Built to Fight AI With AI Raises...
Cybersecurity teams are facing a growing imbalance. Software is being developed and deployed faster than ever, while attackers increasingly use artificial intelligence to automate...
“Shadow AI”: The AI Risk No Firewall Can See
As artificial intelligence tools become part of everyday work, many organizations are discovering a new and largely invisible risk. Employees are increasingly using AI...
Not a Phishing Scam, but Prompt Poaching: How AI Chats Are...
Browser extensions have long been treated as harmless productivity tools, but their growing access to sensitive data is becoming a serious security concern. As...
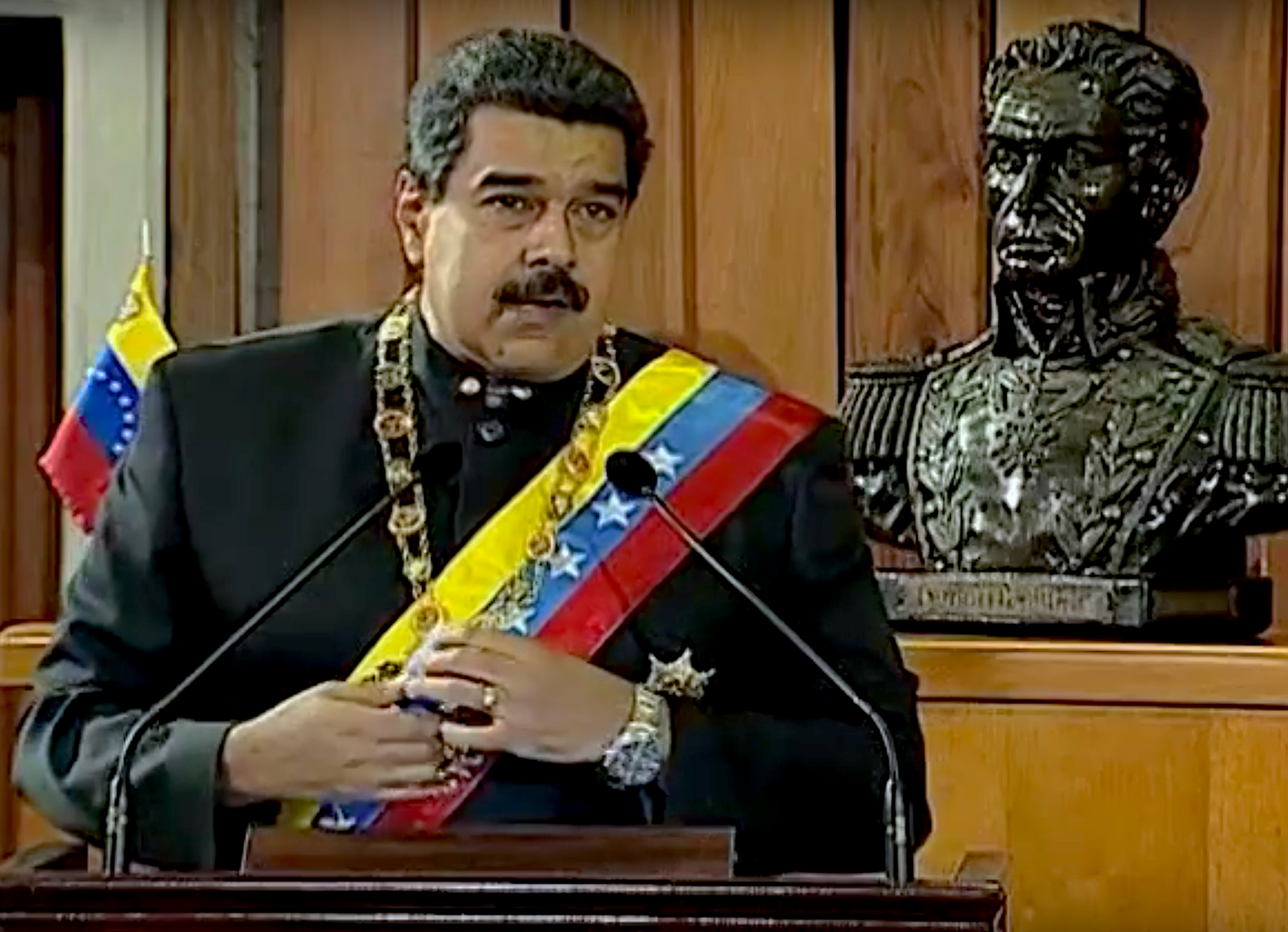
How Cyberattacks Were Used to Open the Door for Military Strikes:...
Cyber operations are increasingly seen as a way to shape the battlefield before the first aircraft or ground unit moves. Power grids, communications networks,...
New AI Protector Helps Vehicles Ignore Fake Signals
As vehicles grow more connected, their internal systems depend on a constant flow of data from sensors monitoring everything from temperature and tire pressure...
Vulnerability Intelligence: The New Operational Weapon in Cyber Defense
In an era where cyber threats evolve at an alarming pace and operational quietude can be disrupted at any moment, the traditional approach to...
This Robot Attack Didn’t Need the Internet in Order to Spread
As humanoid and quadruped robots move from research labs into public spaces, factories, and homes, their growing autonomy is creating a new class of...
This Scam Used Real Cloud Infrastructure to Fool Everyone
Email security teams have long relied on domain reputation and sender verification as their first line of defense against phishing. Messages originating from well-known...
New SIGINT Prototype Aims to Keep Units Connected When Signals Disappear
Modern military operations depend on uninterrupted communication and rapid data sharing, yet many battlefields are anything but cooperative. Urban density, electronic warfare, and natural...
2025 Startups Wrapped: Israeli Tech Draws Bigger Bets as AI Reshapes...
As 2025 draws to a close, Israel’s technology sector is finishing the year with results that look stronger than many expected. This is notable...