Can You Assess IoT Devices Risk?
The Internet of Things (IoT) ecosystem includes a broad variety of devices and device-systems such as power plants, vehicles, home appliances, etc. Its global...
Intriguing Partnership to Advance Security IoT Applications
The Internet of Things (IoT) has been vastly changing safety and security capabilities. By harnessing interconnected technologies and incorporating machine learning and advanced monitoring...
Blockchain to Revolutionize IoT Security
The interconnected smart devices, known as IoT (the Internet of Things), have been an effective tool for home consumers, businesses, and defense markets. However,...
Can You Trust Voice Authentication?
Voice authentication is the practice of logging in to a device or service with your voice alone. Talking to electronics has become a popular—even...
Take Part at The Leading Conference on IoT and Security
The constant growth of technologies enabling the influx of smart connected devices - the Internet of Things (IoT) - has been reflected at the...
Unexpected Solutions Were Showcased at Video Analytics Conference
As every year, the fifth Video Analytics Conference and Exhibition organized by iHLS have gathered the leading experts, developers, entrepreneurs and manufacturers from the...
Call for Proposals for iHLS Security Accelerator Fourth Cycle
Are you developing an innovative technology in one of the following fields?
HLS, unmanned systems and robotics, autonomous vehicles, cyber and information security, border and...
Challenges in Internet-Connected Battlefield
The US military has been facing various challenges in internet-connected, robot-rich congested and contested battlefields. In search for solutions, the U.S. Army Research Laboratory...
Qatar Adopting Smart Airport Technologies
Qatar's Hamad International Airport plans to ramp up biometric solutions alongside other innovations such as VR and robotics on its way to become a...
Pioneering Development Provides Arctic Situational Awareness
A new development in situational awareness technology would support operations in harsh environments such as the arctics. Finnish maritime innovators Fleetrange, a maritime startup and...
Call for Proposals for iHLS Security Accelerator 4th Cycle
Are you developing an innovative product? We can offer you added value in the security market as well.
At the iHLS Security Accelerator, we...
Another Step Towards Making Cities Smarter
The US has been harnessing IoT technologies in attempt to advance a wide array of Smart City applications as well as in response to...
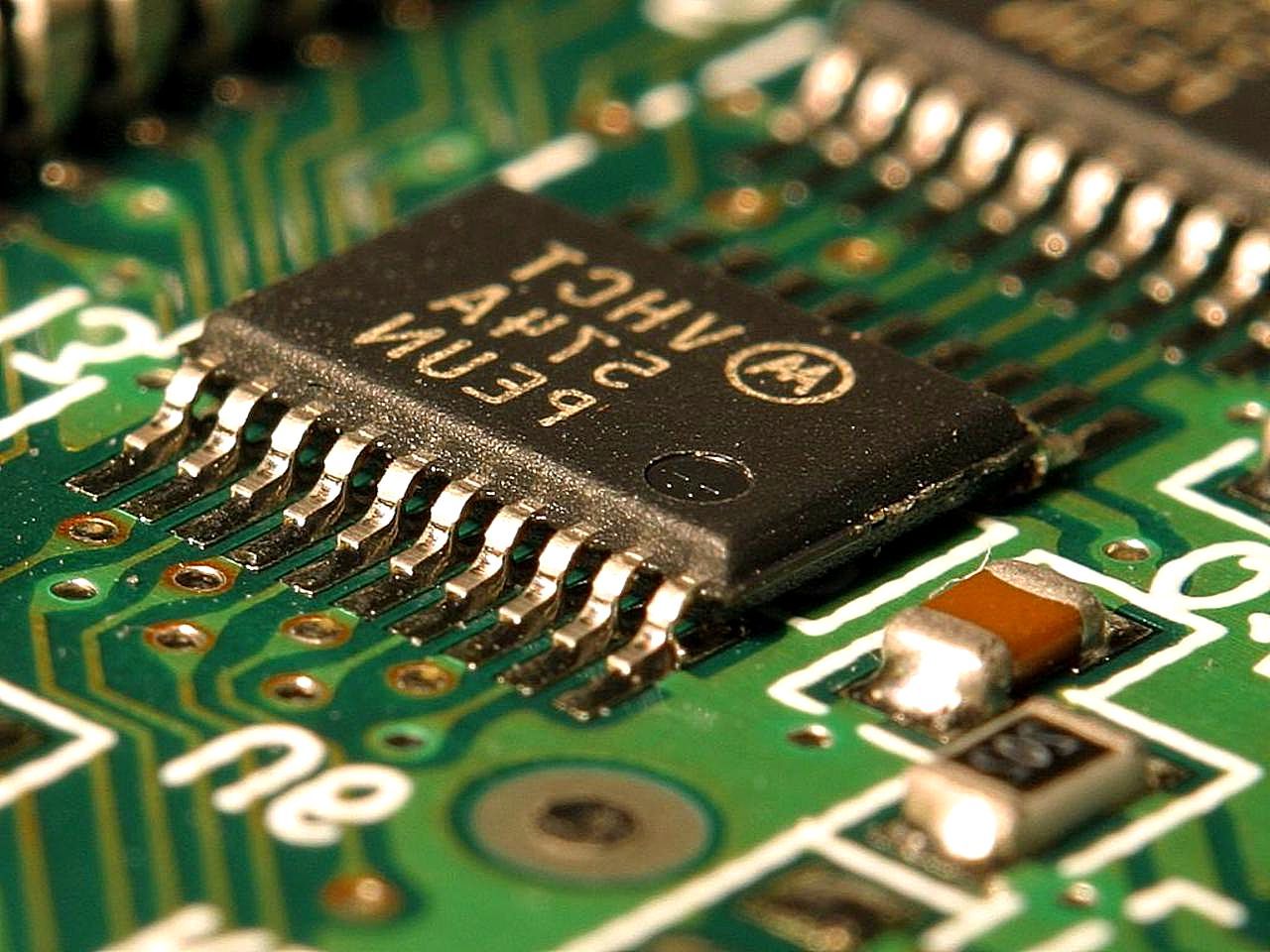
Major Advancement in IT Security from Unexpected Destination
Researchers at New York University Abu Dhabi’s Design for Excellence lab (NYUAD) have developed new innovations in computer chip technology that present landmark achievements...
USB-Connected Devices Are Not Secure As Thought
Security flaws found in USB-connected devices raise questions about the trustworthy of the devices. Apparently, USB connections should be redesigned to offer more security,...
Cyber Security Rules for Autonomous Vehicles Set by UK
The United Kingdom has recently published a set of cyber security regulations, “Key principles of vehicle cyber security for connected and automated vehicles”. The...
Securing The Internet of Things
As IoT matures, applications will be limited only by users’ imaginations. That’s the prediction of Lisa Litherland, a business architect who helps institutions create...
Boost to Biometric Identitiy Market
As organizations search for more secure authentication methods for data access, physical access and general security, many are turning to biometrics. The field has...
Smart City – Convergence of IoT and Video Analytics
When video systems first moved from analogue to digital and then became part of the IoT world, they were primarily used to provide visual...
Smart Cities Need Security Guards As Well
Electricity grid operators in the U.S. experience near constant cyberattacks, with one utility recording approximately 10,000 cyberattacks a month.
Cybersecurity issues can come up...
Catching Up on Evolving Smart City Tech
The Punjab Information Technology Board (PITB), an autonomous body set by the Government of Punjab (a region partly in North India and partly in...
New Dual-Use Video Analytics Platform
A new Video IoT Platform was recently launched by Gorilla Technology at the 2017 International Security Conference (ISC West) in Las Vegas.
The Internet...
New Layer of Defense for IoT Devices
A new layer of defense for IoT devices (the Internet of Things) has been announced. With Cloudflare’s Orbit, IoT manufacturers can add security on...