This post is also available in:
 עברית (Hebrew)
עברית (Hebrew)
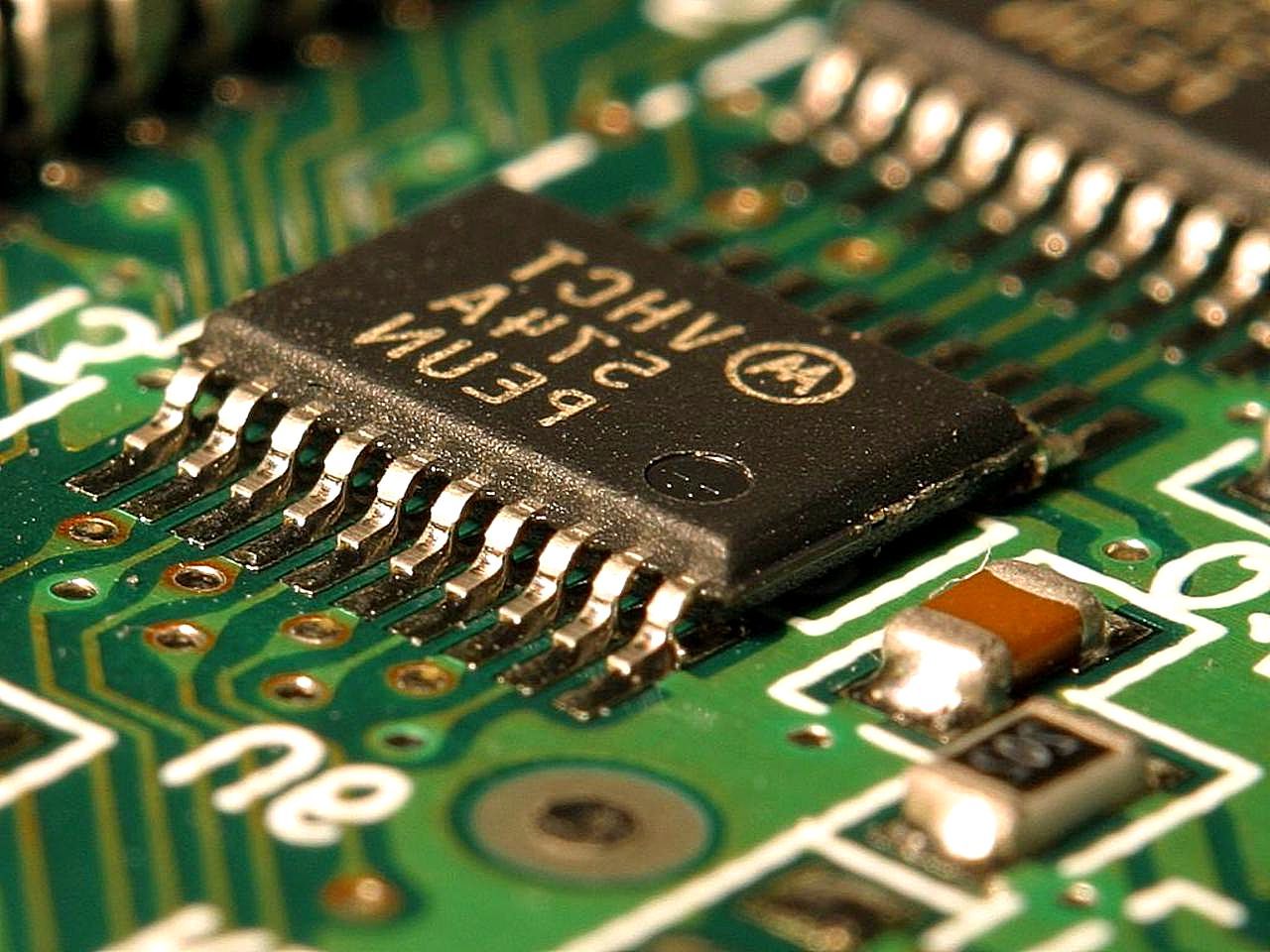
Researchers at New York University Abu Dhabi’s Design for Excellence lab (NYUAD) have developed new innovations in computer chip technology that present landmark achievements in IT security. The development, secured by a secret key so that only authorised users may utilise them, will provide future users with new guarantees of security for their devices.
As IT security rises to the forefront of public concern academic solutions have been investigated in order to secure future systems from hackers. Today, with any electronic device claiming to be “smart” containing a chip, from cell phones and computers to airplanes and medical devices, chip security has become a subject of priority amid the broadening debate surrounding measures for cyber defence.
“Traditionally, security features were implemented at the software or system levels. For the first time, we’ve implemented security at the most basic possible level, the hardware level.
This is important because if the hardware is compromised, there is no software or system security fix,” explained NYUAD Associate Dean of Engineering for Academic Affairs, Associate Professor of Electrical and Computer Engineering, and Head of Design for Excellence, Ozgur Sinanoglu.
“The chip can be unlocked only by loading the secret binary key on its memory. Without it, the chip will not work. Only when the secret key has been loaded will the microprocessor unit inside execute the program loaded on its memory,” he added. NYUAD’s research team designed two different chips over the past year, utilising commercial and in-house developed software tools to help them build a baseline chip as well as their logic-locked chip.
According to emirates247.com, the team at NYUAD is now pursuing a platform that will enable the research community to validate the security of their new solution through extensive testing. “Through their research at NYUAD, the team has surged ahead in the field of solution development for IT security,” Sinanoglu explained.