From Actions to Reactions: A New Training Approach
Military training has traditionally focused on observable outcomes - whether a task was completed correctly or a decision was made on time. But this...
This Portable 5G Tower Brings High-Speed Networks to the Battlefield
Reliable communications remain a persistent challenge in remote and infrastructure-poor environments. Military units, border security teams, and operators working in isolated areas often depend...
The Battle for the Sky Now Depends on Flying Data Hubs
Modern air operations depend heavily on airborne early warning aircraft to detect threats, coordinate forces, and manage complex engagements across large areas. But many...
A Hidden Long-Range Missile Designed to Stay Invisible Until Launch
Modern stealth aircraft are designed around one key principle: avoiding detection for as long as possible. But carrying large external weapons can undermine that...
Tiny Robots, Big Coordination: Learning From Ants
Coordinating large numbers of robots to perform complex tasks remains a major challenge. Traditional systems often rely on centralized control, detailed planning, and constant...
A Visual Intelligence Startup Raised $60 Million
Modern intelligence systems are facing a growing problem: an overwhelming flood of visual information from countless sources, such as security cameras, drones, bodycams, social...
A Smarter Camera That Tracks Movement, Not Frames
Modern sensing systems face a growing challenge: too much data. Traditional cameras capture and process full image frames continuously, even when little is changing...
This Kamikaze Drone Can Strike Targets Almost 1,000 KMs Away
Long-range strike capabilities often face a trade-off between endurance, precision, and survivability. Systems that can reach distant targets may depend heavily on satellite navigation,...
Smarter Signals, Stronger Security: The Next Step in Wireless
As wireless networks evolve toward next-generation standards, they face growing challenges. Higher data rates, denser environments, and increasing interference make it harder to maintain...
A New Tool to Keep Digital Connections Truly Confidential
Invitation-based platforms are widely used to control growth, reduce spam, and build trusted communities. However, they introduce a less visible issue: transparency of social...
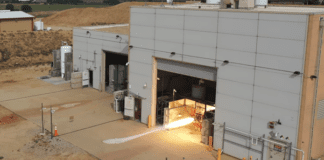
Reusable Rocket Engine Hits Hypersonic Milestone
Hypersonic systems promise significant advantages in speed and responsiveness, but their development has been slowed by a persistent challenge: most propulsion technologies are designed...
Not Just Weapons: AI Is Now Running the Back Office of...
As military systems generate growing volumes of data, managing information has become a challenge in itself. Tasks such as personnel administration, logistics planning, and...
Millions of WhatsApp User Records May Be Circulating on Cybercrime Forums
Large-scale leaks involving phone numbers and messaging accounts are becoming an increasingly common cybersecurity problem. Even when encrypted messaging platforms protect the content of...
Tracking the Untrackable: New Radar Takes on Hypersonic Missiles
Detecting hypersonic missiles remains one of the most difficult challenges in modern air defense. Traveling at speeds above Mach 5, these weapons generate extreme...
A New Layer in Drone Warfare: Launching Strikes From the Sky
Small FPV drones have become a central tool on the modern battlefield, offering precision strike capabilities at relatively low cost. However, their effectiveness is...
First Glimpse: Heavy Bomber Seen With Hypersonic Weapon
As hypersonic weapons development accelerates, one of the key challenges has been integration, meaning how to effectively deploy these large, high-speed systems from existing...
The Small Interceptor Built to Stop Big Drone Threats
The rapid spread of low-cost, one-way attack drones is creating a growing challenge for air defense systems (specifically the Shahed missiles). These platforms are...
Your Face as a Password: The Growing Risk Behind Biometric Security
Facial recognition is quickly becoming part of everyday life. From unlocking phones to passing through airports or entering office buildings, systems that identify individuals...
No Pilot, No Problem: This Helicopter Flies Supplies Into Danger
Supplying forces in contested environments has become increasingly complex. Ground convoys are vulnerable to ambushes and improvised threats, while crewed aircraft face growing risks...
Speed Meets Firepower: The Next-Gen Battlefield Robot
Modern military operations are increasingly defined by speed, flexibility, and reduced risk to personnel. At the same time, forces operating in complex environments, such...
How a Small Interceptor Became a Key Layer in Modern Air...
Short-range aerial threats have become one of the most persistent challenges in modern conflict. Rockets, mortars, and small drones are relatively inexpensive, easy to...
When Your Phone’s Location Data Becomes Evidence
Smartphones constantly generate location data, enabling navigation, ride-sharing, and a wide range of digital services. But that same data is now at the center...