This post is also available in:
 עברית (Hebrew)
עברית (Hebrew)
As 2018 ends, it’s crucial to step back and reflect on some cybersecurity realities. Although US government cybersecurity teams do their best to confront hacking attempts, the lack of time and tight budgets make it difficult to respond to the evolving threat vector. Meanwhile, the attack surface has broadened due to the amount of connected devices and data flowing through organizations – devices and data that many employees need access to in order to get on with their jobs.
Things are probably only to get more complicated in 2019, when the issue of trust will be thrust to the forefront of agencies’ cybersecurity challenges. In 2019, more government agencies will be placing trust in cloud providers to protect their data. They’ll also be placing trust in the individuals that access and manage their data, even as the security of personal biometric data comes into question. Federal government agencies in the US should have on their radar two major threats, according to fifthdomain.com:
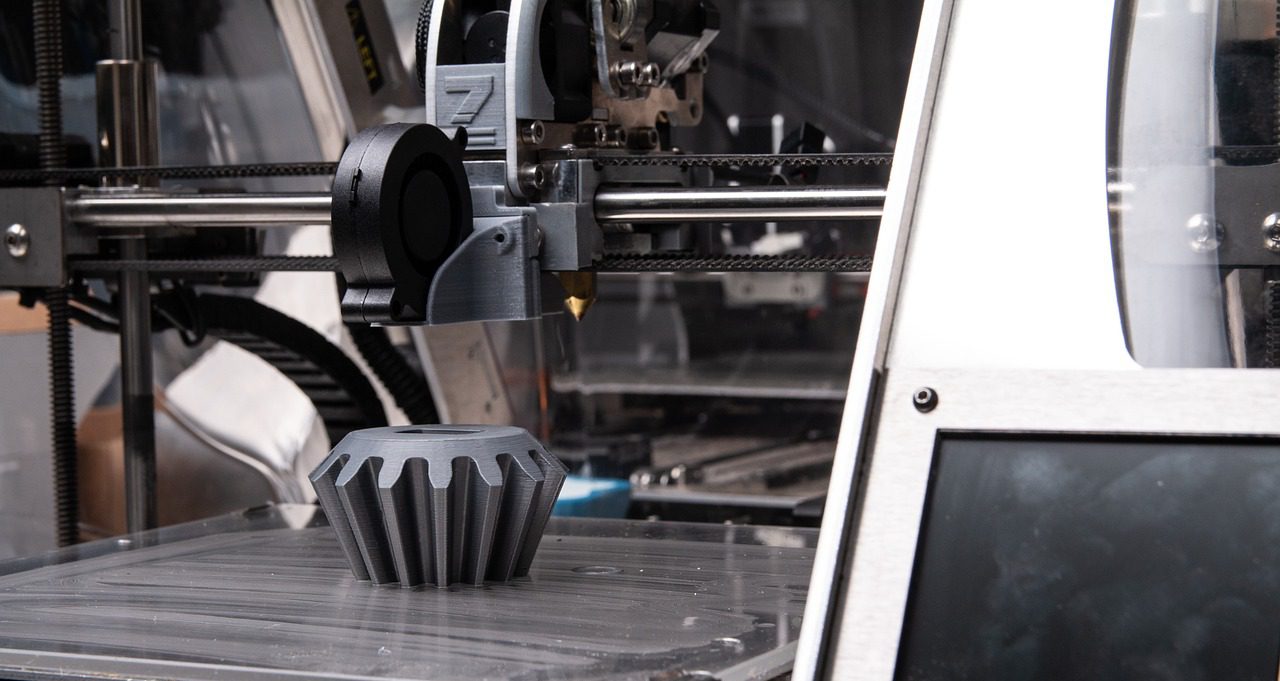
Industrial IoT threat – In 2019, the Internet of Things is going to be among the most challenging area of security. The risk is growing as more devices get connected and as network connectivity moves further to the edge. When such devices are exploited through cloud infrastructure, the result is significant disruptions for governments deploying smart cities and using networks for everything from public transit to disaster management.
In particular, connected devices within manufacturing environments,i.e., the Industrial Internet of Things (IIoT), are extremely desirable targets for attackers, as they offer access to the underlying systems of multi-tenanted, multi-customer environments. As control systems evolve, they are patched, maintained, and managed through cloud service providers. Since processor speed is critical to performance for IIoT, it’s chosen more often over security.
Moreover, many cloud providers simply don’t offer strong enough isolation for a multi-tenant architecture or multi-customer applications, leaving IIoT devices vulnerable. Agencies will need to move from visibility to control where their IT and operational technology networks converge.
Authentication challenge – As biometric and facial recognition software become prime targets for hackers, protecting identity information will continue to be an ongoing challenge in 2019. Email addresses, passwords, and personalized questions are no longer sufficient to protect identities online, but even two-factor authentication and biometric authentication may not be enough. This is especially surprising, because it uses unique data such as fingerprints, movements, and iris recognition. Facial recognition especially has gone mainstream thanks to the Apple iPhone X, but even this seemingly secure technology has serious vulnerabilities.
To combat this, federal agencies should use behavioral biometrics, which provide a continuous authentication layer. Behavioral biometrics recognize identifiers such as mouse movement and scroll speed, which are far harder to mimic, and can be paired with facial recognition or other security measures for layered protection.
In sum, having visibility into the cyber behavior of end-users is crucial to reacting quickly to threats — and to correctly identifying what’s a threat and what’s an employee legitimately trying to get their job done.