Teenagers in the Netherlands Caught Using WiFi Sniffer Near European Law...
Dutch authorities have arrested two 17-year-olds suspected of conducting surveillance near key European law enforcement facilities on behalf of Russian intelligence. The incident is...
Alleged Cyberattack Targets Israeli Satellite Infrastructure, but Claims Raise Doubts
An emerging cyber incident involving Spacecom—the operator of Israel’s AMOS satellite fleet—has drawn attention after a pro-Palestinian hacker group claimed it had gained access...
New Study Finds AI Voice Cloning Now Nearly Indistinguishable from Real...
A new academic study out of Queen Mary University of London has found that AI-generated voices, particularly those created using voice cloning tools, are...
Investigation Finds TikTok Collects Underage Users’ Data
A joint investigation by federal and provincial privacy authorities in Canada has concluded that TikTok’s current measures to prevent children under 13 from using...
New Study Reveals How Encrypted Robot Commands Can Still Leak Sensitive...
As collaborative robots become more common across healthcare and industrial environments, new research highlights a critical gap in how these systems handle privacy—even when...
GitHub Used to Distribute Malware to Mac Users
A recent campaign targeting macOS users is exploiting public trust in well-known software brands by distributing malicious installers through fraudulent GitHub repositories. The attackers...
Massive SIM Card Network Dismantled in Suspected Telecom Disruption Campaign Ahead...
U.S. authorities have uncovered and dismantled a large-scale covert network of electronic devices capable of severely disrupting cellular communications across New York City. The...
North Korean Hackers Use AI-Generated Military ID Deepfakes in Targeted Cyber...
A recent cyber operation linked to North Korea has revealed a new layer of sophistication in the use of artificial intelligence for malicious purposes....
Ransomware Group Claims Breach of U.S. Media Company, Sensitive Data Allegedly...
A ransomware group believed to have links to Russian cybercrime networks has claimed responsibility for a data breach targeting a U.S.-based media company. The...
Cyberattack on European Airport Check-In Systems Continues to Disrupt Operations
A cyber-related incident targeting a key check-in system provider is continuing to affect flight operations across several European airports, with Brussels Airport experiencing the...
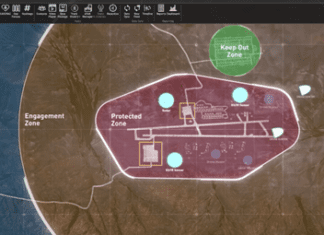
DSEI London 2025 – The Future of International Security: Technology, Collaboration,...
By: Or Shalom
The DSEI London 2025 exhibition, which took place on September 9–12 at the ExCeL Centre in London, is the flagship event for...
The Encryption System that Will Provide Satellite Cybersecurity
The US Space Force has awarded a multi-year contract for the development of an advanced encryption system designed to protect satellite communications from cyber...
Security Researchers Warn: AI Code Assistants Pose Security Threats
AI-powered code assistants have become widely integrated into development environments, improving efficiency through features like code generation, auto-completion and test writing. However, new research...
Liverpool City Council Confirms Ongoing Cyberattacks Linked to Russian Hacker Group
Liverpool City Council has disclosed that it has been the target of sustained cyberattacks over the past two years, primarily from a pro-Russian group...
Wait, this isn’t ChatGPT? Malware Uses Open-Source AI App to Deploy...
Security researchers have identified a new form of malware that uses a seemingly legitimate desktop application based on ChatGPT to install a modular backdoor,...
Malicious Apps Masquerade as WhatsApp and Chrome Through Google Search Manipulation
A new cyberattack technique is using Google Search to distribute malware disguised as widely used applications such as WhatsApp, Telegram, Chrome, and others. Security...
Popular AI Apps Expose Sensitive Data
A security lapse involving Vyro AI, the company behind well-known generative AI apps, has exposed sensitive user data from millions of users. The breach,...
FTC Urged to Probe Microsoft Over Security Practices Linked to Major...
A recent call from U.S. Senator Ron Wyden has renewed scrutiny of Microsoft’s cybersecurity practices, urging the Federal Trade Commission (FTC) to investigate the...
Hidden Cameras Found to Have Critical Vulnerabilities
Millions of consumers using small, internet-connected surveillance cameras may be unknowingly exposing their homes and networks to serious security risks. A recent analysis reveals...
North Korean Hackers Pose as Recruiters to Target Blockchain Professionals Worldwide
A new wave of cyberattacks linked to North Korea has targeted hundreds of individuals globally, with a focus on professionals working in cryptocurrency-related fields....
FTC Flags Children’s Robot App for Unlawful Location Tracking
A U.S. regulatory investigation has concluded that a popular educational robot app unlawfully allowed the collection of children’s location data—without proper parental consent. The...
New Threat Targets Crypto Executives Using Voice Impersonation Tactics
A sophisticated social engineering method targeting the cryptocurrency industry has recently come to light, involving the use of professional voice impersonators to deceive high-ranking...