- home
- News
- Technology
- Cyber
- HLS
- Innovation
- Unmanned
- Video
- Events
- Accelerators
- עברית
- Subscribe
- Contact Us
- home
- News
- Technology
- Cyber
- HLS
- Innovation
- Unmanned
- Video
- Events
- Accelerators
- עברית
- Subscribe
- Contact Us
home More...
More...
Disruptive Tech in Augmented Reality Glasses
Augmented reality (AR) glasses can already do a lot of tasks: Driving along the highway with directions and other pertinent information such as gas...
Nanotechnology to Produce Better Protective Armor
In materials science, enhancing one characteristic of a material will see a decline in a different characteristic. Strength and toughness are a pair like...
Artificial Intelligence to Fight Online Terrorism
Online terrorist content has been fueling violent attacks in recent years. For example, ISIS’s recovering media network has been used to call on its supporters...
Latvian Armed Forces Purchased Rafael’s Spike Missiles
Latvia’s Ministry of Defense signed an agreement for the supply of the Spike missiles developed by Rafael, in a 108 Million Euro deal. The missiles will be...
Uncertainty is Preferable When Drone Navigation is Concerned
Flying drones through cluttered environments like cities is complicated. The ability to avoid obstacles while traveling at high speeds has computational limits, especially for...
Increased Power Supply Without Adding Extra Load
The proliferation of radios, handheld smart devices, GPS, and other personal electronic devices supporting the “future soldier”’s operation has been prompting the examination of...
Flexible Electronics – Rising Star in Wearable Tech Field
A new generation of products is emerging based on low cost printed electronics with embedded silicon ICs and sensors. By eliminating the need for...
How To Make A Drone More Stable In Headwinds
Drones are now everywhere, and being used to do all sorts of missions, that has already been established. Drones can be very useful instruments,...
China is Close To Owning Sci-Fi Like Powered Exoskeletons
Powered exoskeletons are, according to Wikipedia, wearable machines that are mobile and powered using a system of hydraulics, electric motors, pneumatics, levers or a...
New Camera Will Identify IEDs For Soldiers
Soldiers in combat situations have to constantly scan their surroundings for improvised explosive devices (IEDs), a signature weapon of modern guerrilla warfare. These homemade...
HLS Startup Competition in Tel-Aviv: $1 Million Prize to Winning Startups
We are inviting ground-breaking startups in the security, defense and homeland security (HLS) fields to take part in a first-of-its kind startup competition.
iHLS is...
Innovation in Big Data for Geospatial Applications
Servers are increasingly becoming the heart of any geospatial analysis system. All face a similar challenge, whether the system is in the ‘cloud’, a...
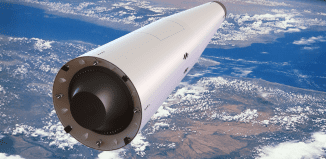
Russia Developing New Multi-Use VTOL Rocket
Russia is now designing a new multi-use VTOL rocket that will also be environmentally friendly.
According to designers, unlike Elon Musk’s Space X Falcon 9,...
Watch: New Anti-Drone Gun To Impose Order In The Sky
In recent years, drones have come a long way from being a rare pastime amateur playing thing to its ubiquity now. Drones are being...
Privacy Solution Found for Location-Aware Devices
The IoT market is experiencing an explosion of GPS-based location-aware devices. However, security and privacy have become serious and significant concerns for consumers of...
New Wearables For Future Forces
Wearable combat tech that’s straight out of a sci-fi movie was developed by Singapore company ST Engineering, and gives us a real life glimpse...
NATO Introduces Cyberspace into Kinetic Battlefield
When the desired target is not directly reachable over cyberspace, the kinetic engagement by military units equipped with the latest technological and tactical advancements...
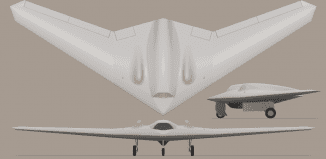
Egozi: The Iranian Reverse Engineering Effort
By Arie Egozi
The Iranian UAS shot down in Israeli territory seems to be part of the reverse engineering efforts made by this country regarding...
Bats Can Help Produce Cheaper Echolocation Sensors
New research from the University of Washington suggests that the Egyptian fruit bat is using similar techniques to those preferred by modern-day military and...
Computer Generated Simulation Upgrades Naval Defense
Military forces use computer simulations to prepare their personnel for real-life situations. The virtual reality technology is gradually used in the military virtual training,...
New Kalashnikov Machine Gun Started Service
Russia was always known as a country that tries to provide itself with all of its security and army needs. This includes everything: ammunition,...
Tech Giant Unveils Big Data Tool for Cybersecurity
A new cybersecurity intelligence and analytics platform has been unveiled. Tech giant Alphabet, the parent company of Google, formed a security company that uses...
Latest
Copyright © 2012 i-HLS. All Rights Reserved.